VENDORiQ: What is Anthropic’s Project Glasswing?
Anthropic’s Project Glasswing debuts autonomous vulnerability discovery, shifting the security paradigm but risking a remediation backlog that demands robust governance.
Anthropic’s Project Glasswing debuts autonomous vulnerability discovery, shifting the security paradigm but risking a remediation backlog that demands robust governance.

Anthropic’s Claude Mythos detects critical vulnerabilities effectively, yet risks overwhelming security teams without automated patching, creating potential national security bottlenecks.
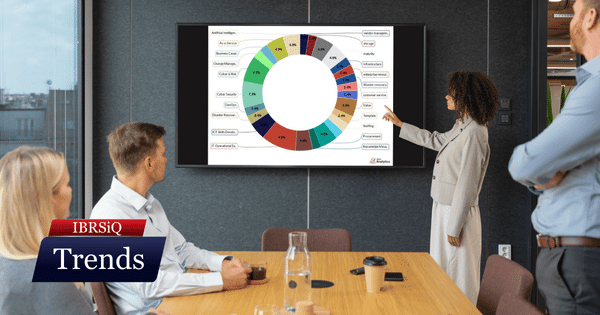
December’s focus shifts toward pragmatic governance, balancing AI adoption and cyber resilience by simplifying processes and prioritising foundational security controls.

To build an effective cyber security strategy, organisations must address human manipulation and physical access risks, not just technical controls and training.

Australia’s new Cyber Security Act, effective May 30, 2025, mandates 72-hour incident and ransomware payment reporting for many organisations, shifting cyber security from operational to compliance.

Chinese AI startup DeepSeek’s impressive, low-cost DeepSeek R1 model has drawn scrutiny over data practices and government ties, leading to an Australian ban on February 4, 2025.

Explore how defining and understanding your organisation’s risk appetite is crucial for developing a sustainable and implementable business continuity plan (BCP), ensuring appropriate investment in cyber security, disaster recovery, and business continuity.

SentinelOne’s Purple AI now integrates with major security platforms like Zscaler and Okta, using AI to automate threat detection and response for improved cybersecurity.